Cybersecurity in the Digital Age
Cybersecurity in the digital age protecting your data against emerging threats is not just about keeping up, it’s about staying ahead. Users like you seek effective ways to ensure cybersecurity
CHECK THIS OUT
Cybersecurity in the digital age protecting your data against emerging threats is not just about keeping up, it’s about staying ahead. Users like you seek effective ways to ensure cybersecurity

Hard drives remain a better way to store and keep data safe. However, there are ways to improve the data safety on hard drives and protect the disk against damage.
Data is the most important asset of any business nowadays; this is a solid reason enterprises offer free-of-charge services like YouTube valuing fortunes. But since data is priceless and targeted
In today’s ever-changing cybersecurity world, one of the most serious concerns that enterprises confront is the insider threat. An insider threat happens when employees misuse their access and privileges to

President Biden recently initiated an executive order to restrict the sale of sensitive personal data to countries including China and Russia. If you’ve been keeping up on privacy headlines recently,

With a cyberattack occurring approximately every 39 seconds, organizations and individuals are understandably concerned about operating in the digital world. That’s why businesses must provide safe options that simultaneously improve

From the explosive popularity of large language models (LLMs) like OpenAI’s ChatGPT to the sweeping commercial adoption of generative AI and machine learning, the AI revolution is picking up momentum.
In today’s digital age, staying cyber-secure in college is more crucial than ever. With the vast amount of personal information stored online, students are prime targets for cybercriminals. Here are

In an era where cyber threats are increasingly sophisticated and pervasive, the paradigm of cloud networking security is undergoing a profound transformation. Central to this change is the adoption of

At a time when cyberattacks are surging and social engineering is the weapon of choice for many cybercriminals, companies increasingly recognize the necessity of cybersecurity awareness training (CSAT). However, too

In an era where cybersecurity and digital privacy are paramount, setting up a VPN on your Mac is a savvy move. A Virtual Private Network (VPN) encrypts your internet connection
In the vast landscape of technology, one aspect that often remains hidden behind the scenes but plays a crucial role in our digital lives is encryption. Encryption ensures our messages,

Companies are rapidly realizing that cybersecurity and physical access control are integral aspects of their daily operations. As the risk of physical threats and cyberattacks increases, the consequences become more

Virtual Private Networks (VPNs) have become an essential tool for anyone who values online privacy and security. They encrypt your internet connection, making it difficult for anyone to intercept your

With so much emphasis behind sharing personal information online for the sake of presenting our best digital selves, we seldom consider the various cyber threats that exist and the propensity

Welcome to another edition of Crypto NFT Today! If you enjoy cryptocurrency, NFTs, and riding emotional rollercoasters, this is the place for you. So put on some soothing music and

With winter holidays now over, many Americans are pleased to have received tech gifts. However, a new gadget also means a new target for hackers looking for victims in the

The specter of cybercrime is perpetually present in the modern age, and it’s a concern for businesses and individuals alike. As such, we all have a responsibility to educate ourselves

There are many tools, platforms, and strategies that seek to mitigate and minimize cyber threats, reducing some of the burden and giving organizations the power to protect themselves from hackers.

The Biden administration recently issued a proclamation that designates November as Critical Infrastructure Security and Resilience Month. At a time when the global economy is still suffering from shortages due
The world of investing is rapidly changing, and one of the most significant changes has been brought about by cybercriminals. The risk of cyberattacks on your business will only increase

By Tri Pham – CEO of Whydah, Co-Founder of KardiaChain Long before DeFi became popular, the gaming industry was already doing exceptionally well. Today, the DeFi TVL stands at $222

How Businesses Can Stem the Tide of eCommerce Fraud By Arnab Banerjee, Lead System Architect eCommerce fraud is a plague that strikes at the heart of all online commerce and

By Zack Schuler, founder and CEO of NINJIO Cybercriminals are experts at exploiting vulnerabilities. While security tools are constantly improving, cybercriminals’ tactics evolve right along with them – a process

A business needs to protect its customers from identity theft, not only because it can significantly impact your customers’ lives, it can have severe effects on your business as well.

There are few businesses today that aren’t in some way reliant on technology. Our digital age has produced tools with which to work more efficiently and introduced entirely new industries

By Zack Schuler, founder and CEO of NINJIO When it comes to cybersecurity, companies are in the middle of a trust crisis – every day, consumers are becoming more acutely

Cybersecurity strategies traditionally secure the company network against outsider interference. However, as a new wave of data protection laws swept the globe, organizations became legally liable for the protection of

Atlas VPN’s analysis reveals that phishing in the US soared over 12 times in the last five years, hitting a record 241,342 complaints in 2020. This data is provided by

Cloud computing has become mainstream. Companies are adopting it because it is scalable and flexible. Businesses can use it in testing and development environments as well as to store, manage

Cloudrise conquered the seemingly impossible in 2020, launching a new company amid a pandemic and economic downturn. Despite those challenges, their hard work paid off and Cloudrise is reporting a

This post is sponsored content. A lot of companies at this point work with dispersed workers and little or no office space, and with the worldwide health crisis forcing even
While automation and the use of robotics has drastically increased the efficiency of manufacturing processes, logistics, and delivery, the casualty list for a slew of manual and service-based jobs on and off the production line is growing.

Amazon is no stranger to controversy when it comes to employee conditions and relations. Through protests, strikes and walkouts, the company has seen workers stand up and demand fair treatment. Recent breaking news regarding surveillance of employees has now reignited that controversy. In the United Kingdom, union groups and activists are demanding action against Amazon’s latest move.

Are you thinking about moving your data to the cloud?
Perhaps you have a lot of employees working from home currently. Emailing files to one another isn’t a workable solution for long … but you might also be concerned about moving to the cloud.

Public safety and the justice system are two growing areas of interest for citizens and police in the United States. Between political and racial tensions, unrest has been on the rise in drastic ways this year. Specifically, government officials and civil rights activists have turned a spotlight on police violence. More than ever, people are questioning how helpful or hurtful predictive policing is in today’s society.

In this digital world where everyone is hooked on the latest technological devices, the concept of IoT (Internet of Things) is at the forefront of all industries. A lot of IoT devices like your company’s thermostats, security systems, vending machines, lights, and more rely on this kind of connectivity.

Today we live in a world that is entirely driven by technology, and getting any work done requires plenty of dependencies on the internet. These days the gateway to someone’s life is through their electronic devices, whether it be their phones, computers, or even their MP3 players. Applications like Facebook, WhatsApp, Instagram, Twitter, Snapchat, freeaccount.one and TikTok have all risen to popularity over the last decade tremendously. Even though questions regarding their privacy issues and lack of security have often done the rounds, it still has not stopped their immense popularity.

First developed in 1971, File Transfer Protocol (FTP) servers have long served a key part in data communication. Before the advent of Transfer Connection Protocol (TCP) and Internet Protocol (IP),
Facial recognition has always been a controversial technology, especially when it comes to the government using it. As tensions between the public and police have risen, some big names in
Cybersecurity in the digital age protecting your data against emerging threats is not just about keeping up, it’s about staying ahead. Users like you seek effective ways to ensure cybersecurity

Hard drives remain a better way to store and keep data safe. However, there are ways to improve the data safety on hard drives and protect the disk against damage.
Data is the most important asset of any business nowadays; this is a solid reason enterprises offer free-of-charge services like YouTube valuing fortunes. But since data is priceless and targeted
In today’s ever-changing cybersecurity world, one of the most serious concerns that enterprises confront is the insider threat. An insider threat happens when employees misuse their access and privileges to

President Biden recently initiated an executive order to restrict the sale of sensitive personal data to countries including China and Russia. If you’ve been keeping up on privacy headlines recently,

With a cyberattack occurring approximately every 39 seconds, organizations and individuals are understandably concerned about operating in the digital world. That’s why businesses must provide safe options that simultaneously improve

From the explosive popularity of large language models (LLMs) like OpenAI’s ChatGPT to the sweeping commercial adoption of generative AI and machine learning, the AI revolution is picking up momentum.
In today’s digital age, staying cyber-secure in college is more crucial than ever. With the vast amount of personal information stored online, students are prime targets for cybercriminals. Here are

In an era where cyber threats are increasingly sophisticated and pervasive, the paradigm of cloud networking security is undergoing a profound transformation. Central to this change is the adoption of

At a time when cyberattacks are surging and social engineering is the weapon of choice for many cybercriminals, companies increasingly recognize the necessity of cybersecurity awareness training (CSAT). However, too

In an era where cybersecurity and digital privacy are paramount, setting up a VPN on your Mac is a savvy move. A Virtual Private Network (VPN) encrypts your internet connection
In the vast landscape of technology, one aspect that often remains hidden behind the scenes but plays a crucial role in our digital lives is encryption. Encryption ensures our messages,

Companies are rapidly realizing that cybersecurity and physical access control are integral aspects of their daily operations. As the risk of physical threats and cyberattacks increases, the consequences become more

Virtual Private Networks (VPNs) have become an essential tool for anyone who values online privacy and security. They encrypt your internet connection, making it difficult for anyone to intercept your

With so much emphasis behind sharing personal information online for the sake of presenting our best digital selves, we seldom consider the various cyber threats that exist and the propensity

Welcome to another edition of Crypto NFT Today! If you enjoy cryptocurrency, NFTs, and riding emotional rollercoasters, this is the place for you. So put on some soothing music and

With winter holidays now over, many Americans are pleased to have received tech gifts. However, a new gadget also means a new target for hackers looking for victims in the

The specter of cybercrime is perpetually present in the modern age, and it’s a concern for businesses and individuals alike. As such, we all have a responsibility to educate ourselves

There are many tools, platforms, and strategies that seek to mitigate and minimize cyber threats, reducing some of the burden and giving organizations the power to protect themselves from hackers.

The Biden administration recently issued a proclamation that designates November as Critical Infrastructure Security and Resilience Month. At a time when the global economy is still suffering from shortages due
The world of investing is rapidly changing, and one of the most significant changes has been brought about by cybercriminals. The risk of cyberattacks on your business will only increase

By Tri Pham – CEO of Whydah, Co-Founder of KardiaChain Long before DeFi became popular, the gaming industry was already doing exceptionally well. Today, the DeFi TVL stands at $222

How Businesses Can Stem the Tide of eCommerce Fraud By Arnab Banerjee, Lead System Architect eCommerce fraud is a plague that strikes at the heart of all online commerce and

By Zack Schuler, founder and CEO of NINJIO Cybercriminals are experts at exploiting vulnerabilities. While security tools are constantly improving, cybercriminals’ tactics evolve right along with them – a process

A business needs to protect its customers from identity theft, not only because it can significantly impact your customers’ lives, it can have severe effects on your business as well.

There are few businesses today that aren’t in some way reliant on technology. Our digital age has produced tools with which to work more efficiently and introduced entirely new industries

By Zack Schuler, founder and CEO of NINJIO When it comes to cybersecurity, companies are in the middle of a trust crisis – every day, consumers are becoming more acutely

Cybersecurity strategies traditionally secure the company network against outsider interference. However, as a new wave of data protection laws swept the globe, organizations became legally liable for the protection of

Atlas VPN’s analysis reveals that phishing in the US soared over 12 times in the last five years, hitting a record 241,342 complaints in 2020. This data is provided by

Cloud computing has become mainstream. Companies are adopting it because it is scalable and flexible. Businesses can use it in testing and development environments as well as to store, manage

Cloudrise conquered the seemingly impossible in 2020, launching a new company amid a pandemic and economic downturn. Despite those challenges, their hard work paid off and Cloudrise is reporting a

This post is sponsored content. A lot of companies at this point work with dispersed workers and little or no office space, and with the worldwide health crisis forcing even
While automation and the use of robotics has drastically increased the efficiency of manufacturing processes, logistics, and delivery, the casualty list for a slew of manual and service-based jobs on and off the production line is growing.

Amazon is no stranger to controversy when it comes to employee conditions and relations. Through protests, strikes and walkouts, the company has seen workers stand up and demand fair treatment. Recent breaking news regarding surveillance of employees has now reignited that controversy. In the United Kingdom, union groups and activists are demanding action against Amazon’s latest move.

Are you thinking about moving your data to the cloud?
Perhaps you have a lot of employees working from home currently. Emailing files to one another isn’t a workable solution for long … but you might also be concerned about moving to the cloud.

Public safety and the justice system are two growing areas of interest for citizens and police in the United States. Between political and racial tensions, unrest has been on the rise in drastic ways this year. Specifically, government officials and civil rights activists have turned a spotlight on police violence. More than ever, people are questioning how helpful or hurtful predictive policing is in today’s society.

In this digital world where everyone is hooked on the latest technological devices, the concept of IoT (Internet of Things) is at the forefront of all industries. A lot of IoT devices like your company’s thermostats, security systems, vending machines, lights, and more rely on this kind of connectivity.

Today we live in a world that is entirely driven by technology, and getting any work done requires plenty of dependencies on the internet. These days the gateway to someone’s life is through their electronic devices, whether it be their phones, computers, or even their MP3 players. Applications like Facebook, WhatsApp, Instagram, Twitter, Snapchat, freeaccount.one and TikTok have all risen to popularity over the last decade tremendously. Even though questions regarding their privacy issues and lack of security have often done the rounds, it still has not stopped their immense popularity.

First developed in 1971, File Transfer Protocol (FTP) servers have long served a key part in data communication. Before the advent of Transfer Connection Protocol (TCP) and Internet Protocol (IP),
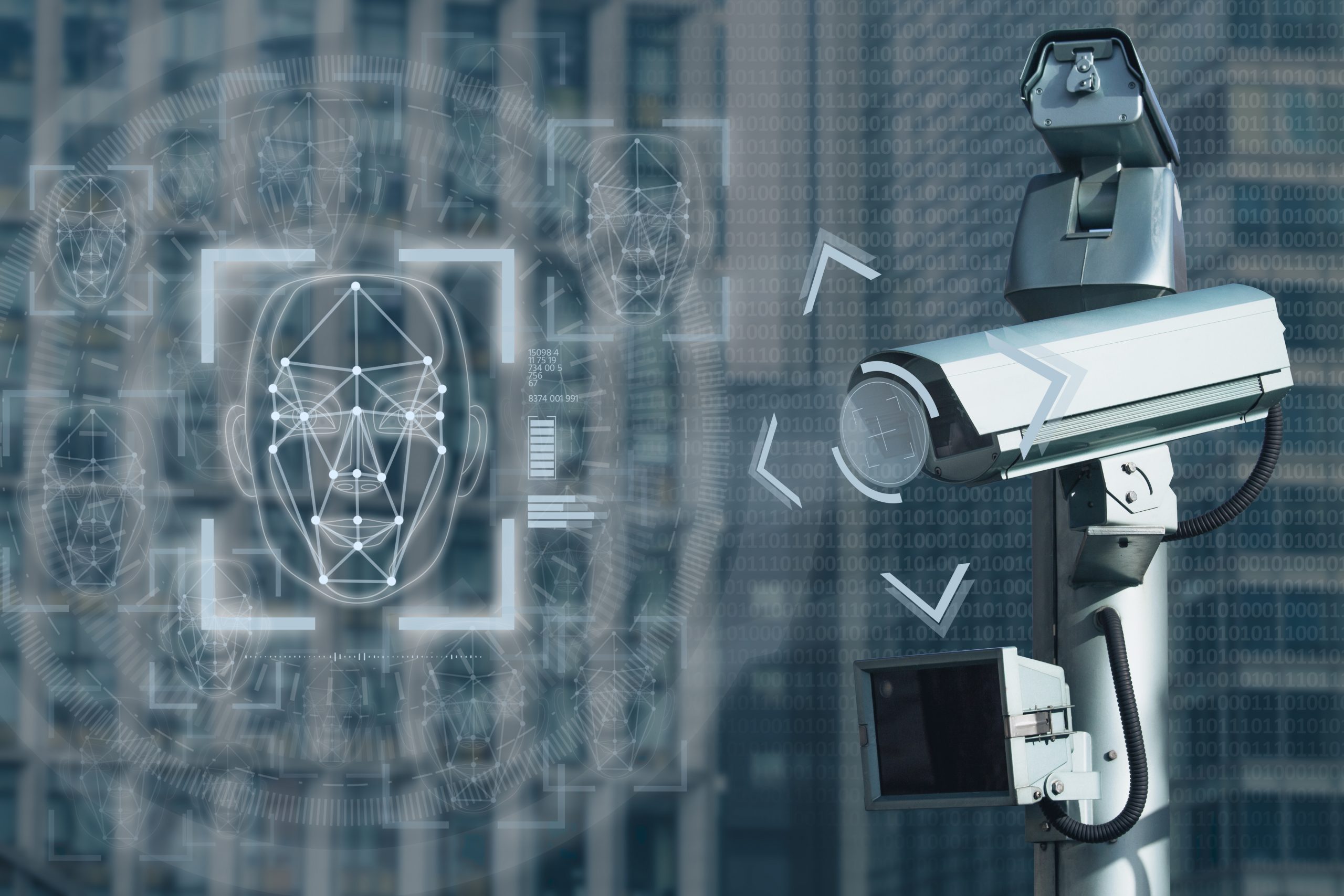
Facial recognition has always been a controversial technology, especially when it comes to the government using it. As tensions between the public and police have risen, some big names in
©Innovation & Tech Today 2024. All rights reserved.