In the early 1940s, the world was facing an emerging threat: the atomic bomb. The United States and its allies believed the Germans were close to completing a nuclear weapon of mass destruction, something not seen before in human history.
The first letter Albert Einstein wrote to President Franklin D. Roosevelt in 1939 provided support for the enrichment of uranium for national defense purposes.
However, Einstein wrote a second letter in 1945, in which he expressed his fear that the world was heading down a slippery slope. In other words, the 20th century’s greatest mind had foreseen what was in motion and it made him tremble.
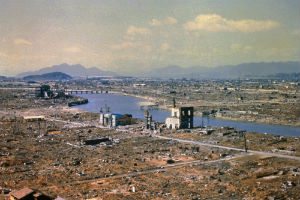
Ultimately, America launched the only nuclear attacks in world history. Regardless of whether the decision was right or wrong, the results were devastating.
Seventy-two years later, and we’re facing a new pivotal era of weapons development: cyber warfare.
Initially, hacking was a curiosity for a small group of computer experts with a unique skillset. The question was simply, “Can I break in?” This evolved over time, and the questions became more nefarious. “What can I access?” “What can I steal?” “What can I destroy?”

The creation of Stuxnet continued to up the ante, as the virus was used against a nation-state (Iran) during the Bush administration in the 2000s for the purpose of disabling nuclear capability. With this new form of assault, a nuclear facility was placed at risk along with all of its workers and the surrounding population.
It is widely believed that the Stuxnet code was re-engineered by other hacker groups, which created a potential threat to the very same nation (the U.S.) that created it as well as a host of others that had no dog in the fight.
This once uncommon occurrence has led to a paradigm of global cyber warfare. It is a new era, with players working to create the most harmful code possible – the equivalent of a nuclear arms race. Unlike a nuclear missile, however, the tools created by nation states are not secured. Look at the recent NSA leak of state-of-the-art malicious code (aka cyber weapons) now being reverse-engineered by the very same hackers the code was designed to combat. Someone, somewhere, has created the cyber equivalent of “Fat Man” and “Little Boy.” In fact, there were devastating financial institution and electric power grid attacks transpiring in the Ukraine in mid-2017.

Despite the growing awareness of these threats, cyber warfare is still a wild west. There are not enough educated committees in government, commerce, or academia to properly make decisions as to the “rules of engagement.” This is problematic as even in “real” war, there are global agreements that outline such rules and the strict repercussions for breaking them. The International Atomic Energy Agency – the nuclear watchdog of the United Nations – exists for the purpose of keeping the world as safe as possible in this nuclear age. However, there is no international “Cyber Agency,” which leaves a void in an area in deep need of oversight. With rogue nation states increasingly conducting cyber warfare, the world needs global experts to ensure total chaos does not break out. And we need it now before the cyber equivalent of “Fat Man” is unleashed.
It may seem like a stretch to some people to compare cyber warfare to nuclear capability. But we are in uncharted territory. There is no reason to think that if power grids, supervisory control and data acquisition (SCADA) systems, and hydroelectric plants can be hacked, that it can’t happen to nuclear facilities, including silos. In my opinion, “The Internet of Things is the Internet of Threats.” If a device is connected, it is vulnerable. Period. Most information technology (IT) professionals struggle with asset management, much less truly understanding the security posture of their organizations.

The underlying message here is that we don’t always understand our own infrastructure. And we don’t always understand the associated vulnerabilities and threats. As security professionals, we have to get it right every time. The hacker only has to get it right once. And if this singular incident happens to occur at a nuclear facility or silo, then we are up the proverbial creek.
It’s up to computer scientists to start contacting and educating those responsible for formulating policy in this regard. Because, right or wrong, we are going down a dangerous path from which there may be no return.
Shawn R. Key is the CEO and President of 21st Century Technologies, Inc., a HUBZone certified, small business cybersecurity company based in Luray, Virginia. He currently heads the training certification program at Stratford University. Read our full interview with Shawn R. Key.
Photo Credits: Featured Image – Courtesy of Pixabay. (1) The aftermath of Atomic Bomb “Little Boy” Hiroshima Japan 1945 “Courtesy of History.com” (2) A Siemens S7 PLC unit, using the same software targeted by the Stuxnet virus. (3) Missle in Silo Courtesy of Dreamstime. (4) Anti-aircraft weaponry protects the Natanz Nuclear Facility in Iran.
By Shawn Key









